When latency hit our authentication gate at 02:14 GMT, it wasn't a bug—it was a protocol.
We traced the incident to a misconfigured data retention rule that triggered a cascade of token invalidations. The fix wasn't just patching a server; it was rethinking how we handle session metadata in transit. That moment defines our approach to privacy: not as a compliance checkbox, but as an architectural principle woven into every data flow.
The Data Covenant: Our Three Unbreakable Rules
We don't treat privacy as a separate layer. It's the substrate. These principles guide every engineering decision and client interaction.
Encryption by Default, Not by Configuration
All data in transit and at rest is encrypted with AES-256. Our key management is isolated from application code, and we rotate keys every 90 days automatically. There is no "unencrypted mode" in our infrastructure.
Data Minimization as a Performance Metric
We only collect what is strictly necessary for service delivery. Each data point has a defined TTL (Time To Live). Retention policies are enforced at the database level, not in code, preventing accidental creep.
Transparency as an Operational Cost
We provide clear, real-time logs of data access. Any client can request a full audit trail of their data within 24 hours. This isn't just a GDPR right; it's a system capability we designed from day one.
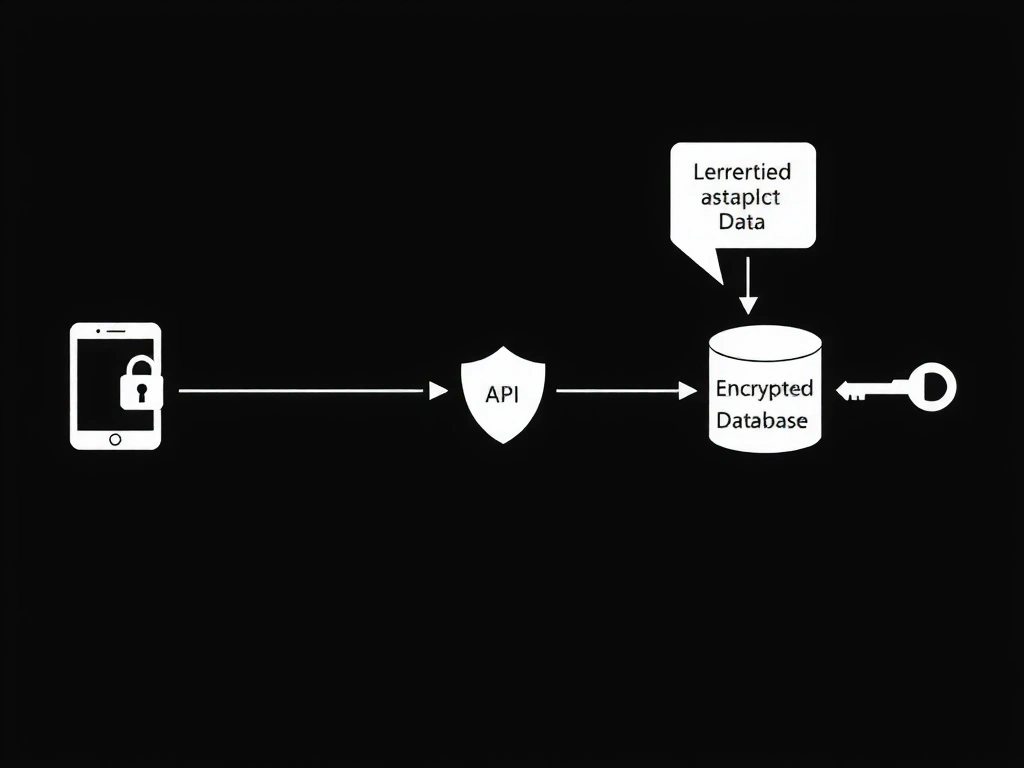
End-to-End Encryption & Access Path
How Your Data Travels
Your data never touches a disk in plaintext. From the moment it enters our API gateway until it's served for analytics, it's protected by a chain of cryptographic trusts. We've modeled our data flow on zero-trust network principles, segmenting services to minimize blast radius.
Client-Side Hashing
Sensitive identifiers are hashed in the client application before transmission, adding an extra layer of protection.
TLS 1.3+ & Certificate Pinning
All connections use the latest TLS standard. We pin certificates to prevent man-in-the-middle attacks, even from trusted CAs.
At-Rest Encryption with Customer Key
Database records are encrypted with keys managed in a separate Hardware Security Module (HSM). We cannot access your raw data without your explicit consent.
Common Architectural Pitfalls (And How We Avoid Them)
The "Logging Lockdown" Trap
The Mistake: Over-logging PII (Personally Identifiable Information) "just in case" for debugging. This creates a massive, ungovernable data sprawl that's a breach waiting to happen.
Our Approach: We log with structured, anonymized metadata. Sensitive fields are redacted at the source. Debugging uses correlation IDs, not user identifiers. We maintain a 30-day log retention by default.
Third-Party Service Blind Trust
The Mistake: Relying on SaaS analytics or customer support tools that request full access to your user data, creating a hidden data pipeline you don't control.
Our Approach: We conduct security audits of all third-party integrations. Data sharing is minimized via API scopes. For analytics, we host our own instance of open-source tools, keeping data within our control boundary.
The "Right to be Forgotten" Ambiguity
The Mistake: Treating deletion as a simple database `DELETE` command, but leaving traces in backups, caches, or replicated systems.
Our Approach: We implement cryptographically secure deletion. Requests are propagated to all replicas and backup systems within our 24-hour compliance window. We provide a certificate of destruction for enterprise clients.
Compliance & Frameworks
Our privacy and security practices are mapped to leading international standards. This isn't just for marketing; it's the framework we use to audit our own systems quarterly.
For Enterprise Clients
We provide Data Processing Agreements (DPAs) and can sign custom processing terms. Our systems are designed for easy auditability.
Request a DPA →Contact Our Data Protection Officer
Address
Via Roma 123, 00100 Roma, Italy
Phone
+39 06 12345678
info@dataviox.pro
Working Hours
Mon-Fri: 9:00-18:00 CET